In enterprise network design, firewall placement is misclassified as a simple "topology issue," but in practice, it is a multifaceted challenge—balancing security principles, network scale, operational complexity, and maintenance capabilities.
Many enterprises undergo a predictable evolution in their security posture:
- Initial Phase: Firewalls are naturally placed at the Internet edge.
- Expansion Phase: As internal lateral threats increase, organizations reconsider adding protection at the core layer.
- Modern Phase: With the adoption of cloud migration and Zero Trust Architecture (ZTA), the traditional debate of "edge vs. core" evolves into a more holistic security strategy.
This article delves into the evolution of real enterprise networks to explore where firewalls should be deployed to maximize their defensive value.
1. Traditional Enterprise Firewall Deployment Models
Based on current enterprise architectures, firewalls are typically positioned in two primary locations: the network edge and the network core layer. Before evaluating specific architectures, we must clarify the functional distinctions between these two deployment modes.
1.1 Edge Firewalls (Perimeter Security)
Core firewalls are deployed at the heart of the internal network to govern traffic between different security zones (East-West traffic).

Core Firewalls Typical Topology
Core Responsibilities in this Architecture:
- Egress Filtering: Managing internal host access to internet resources.
- Inbound Defense: Blocking external scanning, penetration attempts, and DDoS attacks originating from the internet.
- Edge Services: Handling NAT (Network Address Translation), port mapping, and SSL/IPsec VPN termination.
1.2 Core Firewalls (Internal Segmentation)
Core firewalls are deployed at the heart of the internal network to govern traffic between different security zones (East-West traffic).
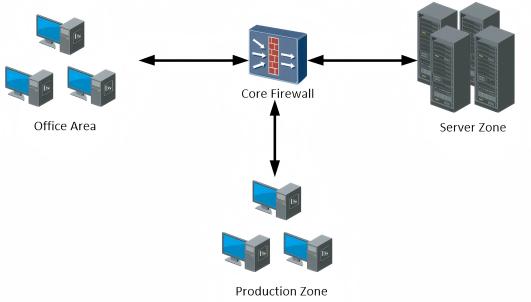
Core Firewalls Typical Topology
Core Responsibilities in this Architecture:
- Logical Isolation: Establishing security boundaries between office zones, Server Zones (DMZ), and production environments.
- Lateral Movement Prevention: Preventing attackers from moving freely between internal network segments after compromising an endpoint.
- Granular Control: Implementing targeted security auditing and access control based on specific business data flows.
2. Why Firewalls are Traditionally Deployed at the Edge?
The long-standing dominance of edge-centric deployment is no accident; it is the result of historical context, cost structures, and operational simplicity.
2.1 The "Fortress" Mentality
In the early days of networking, threats were primarily external. Under the philosophy of "keeping the enemy at the gate," as long as the perimeter was secured, the internal network was treated as a trusted zone.
2.2 Cost-Efficiency
High-performance core firewalls are capital-intensive. For SMEs (Small and Medium Enterprises), a single edge firewall should simultaneously address security, NAT, and VPN requirements, delivering 80% of the security benefits within a limited budget.
2.3 Operational Simplicity
Edge policies typically follow a "Permit Outbound, Deny Inbound" logic. This clarity minimizes the risk of business disruption caused by configuration errors and ensures clear lines of responsibility.
3. Why Single Perimeter Security Is No Longer Sufficient
3.1 Stealthy and Internalized Attack Vectors
Modern cyber threats—such as Ransomware and APT (Advanced Persistent Threats)—often breach the internal network via phishing emails or supply chain vulnerabilities. Once an internal PC is compromised, the attack moves laterally. Since this "East-West traffic" never crosses the perimeter, it remains entirely invisible to edge devices.
3.2 Exploding Internal Network Complexity
Modern enterprise networks are no longer "flat." They comprise multiple dimensions: office networks, production lines, database zones, and third-party access points. Without core isolation, a breach in a low-security area (like a test environment) allows an attacker to move laterally unimpeded, directly targeting core databases.
3.3 Compliance and Auditing Requirements
As global regulatory frameworks mature, "Least Privilege Access" and "Traffic Auditing" between critical business segments have become mandatory. These granular requirements cannot be met by a firewall sitting at the network boundary.
4. Practical Challenges of Core Firewall Deployment
While internal segmentation is vital, simply moving firewalls to the core layer is not a panacea; it introduces new technical challenges:
4.1 The Performance Bottleneck
The core layer handles massive volumes of East-West traffic and is extremely latency-sensitive. If a firewall's throughput or concurrent session capacity is insufficient, the security appliance becomes a performance disaster.
4.2 Network Architecture Complexity
Introducing core firewalls requires restructuring VLANs, routing protocols, and security zone mappings. This leads to an exponential increase in policy configurations.
4.3 Operational Risks
A minor error in a core policy can cause widespread business outages. The long troubleshooting chain demands a high level of expertise from the IT operations team.
5. Building a Layered Defense Architecture
Firewall deployment should not be a binary choice between "Edge" or "Core." Instead, enterprises should build a layered defense system based on their specific scale:
- Layer 1: The Perimeter Edge Layer. Keep it focused on NAT, VPN termination, and baseline boundary protection.
- Layer 2: The Regional Core Layer. Establish security zones. Deploy firewalls between the office network and core business segments to restrict any potential breach to a "Minimum Blast Radius."
- Layer 3: Host and Application Layer. Integrate Micro-segmentation, Zero Trust Architecture (ZTA), or Cloud Security Groups. This ensures that even if the network is penetrated, core assets retain self-defense and recovery capabilities.
6. Selection Recommendations by Enterprise Scale
| Enterprise Scale | Recommended Firewall Strategy | Core Objectives |
|---|---|---|
| Small Enterprises (< 200 employees) | Single Edge Firewall + VLAN Logical Isolation | Minimalist Operations: Focus on basic perimeter defense to ensure the network is not "exposed" to the public web. |
| Medium Enterprise (200–1,000 employees) | Edge Firewall + Core Zone Segmentation | Balanced Defense: Securing the perimeter while blocking lateral movement within internal segments. |
| Large Enterprise (> 1,000 employees) | Multi-layer Tiered Deployment + Zero Trust / Micro-segmentation | Total Visibility: Implementing a default distrust with full traffic visibility. |
 English
English
